Today we are excited to release our solution to conveniently send cryptocurrency to any email address.
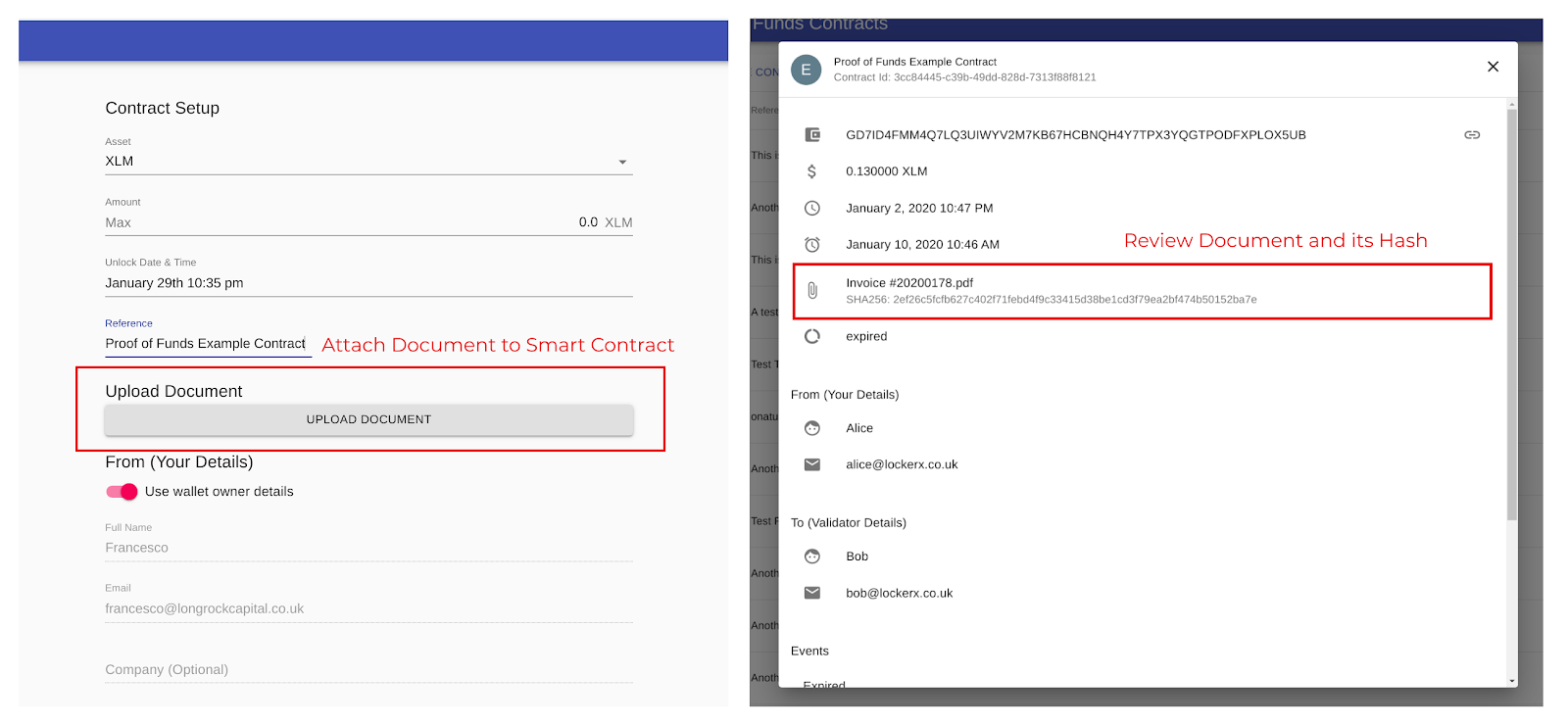
To start sending bitcoin to any email address, simply head to flash.lockerx.co.uk . On this page, you can choose the amount and crypto you want to send, together with the other person’s email address and your signature and email. We use this information to keep you up-to-date with the status of your payment by email.
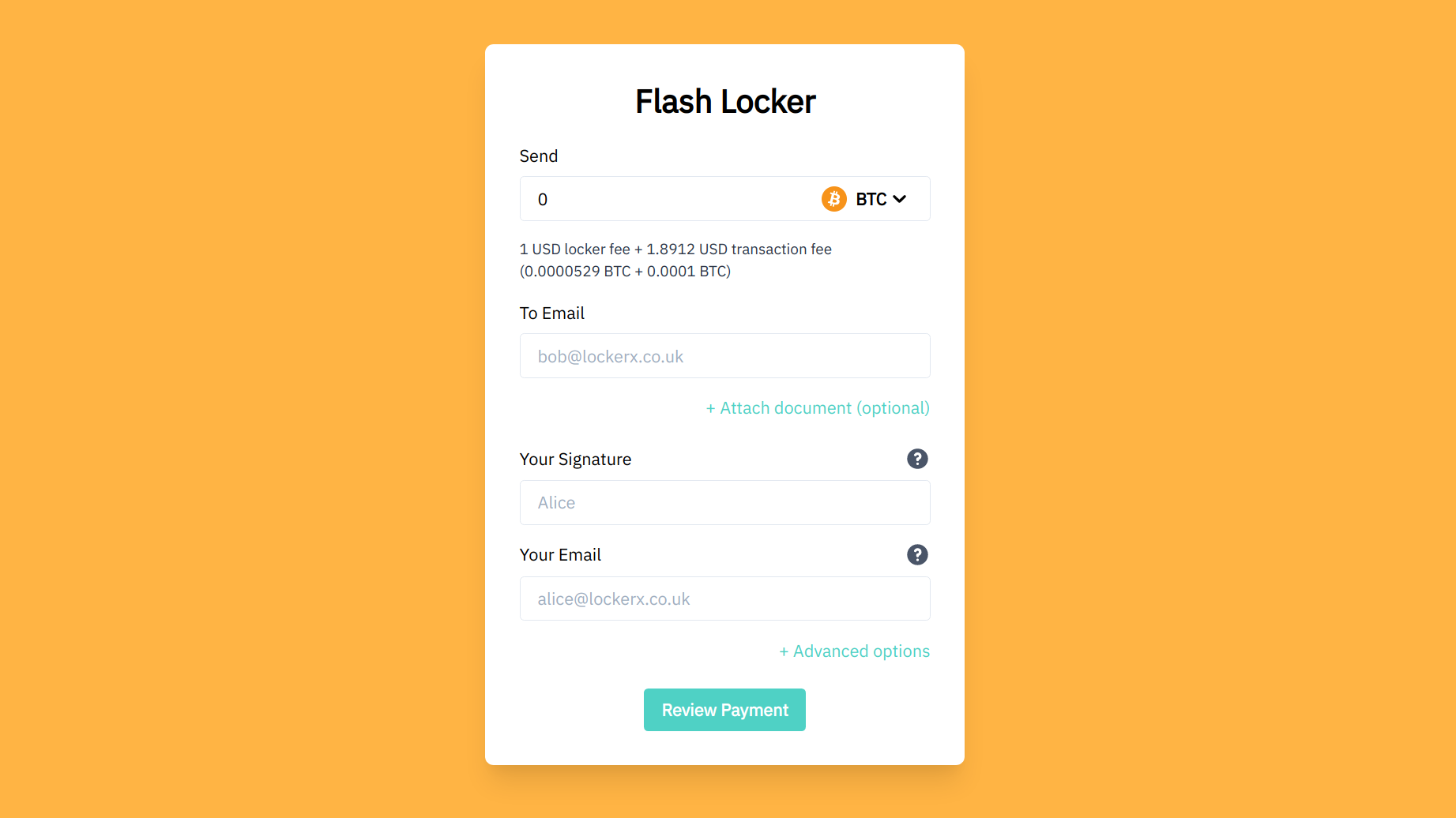
After filling out your details and clicking “Review Payment”, you can review the information you provided. On this page, you can find the secret unlock code that we will email to the other person.
After confirming your details, LockerX starts creating your smart contract and locking it so that only the other person can unlock it using their secret unlock code. When the contract is locked, you’re asked to send your bitcoin payment to it, at this point only the person with the secret unlock code can withdraw the funds. After you deposited your crypto, LockerX emails the other person to inform them of your payment.
The other person simply has to visit the link LockerX sends them to claim their payment.
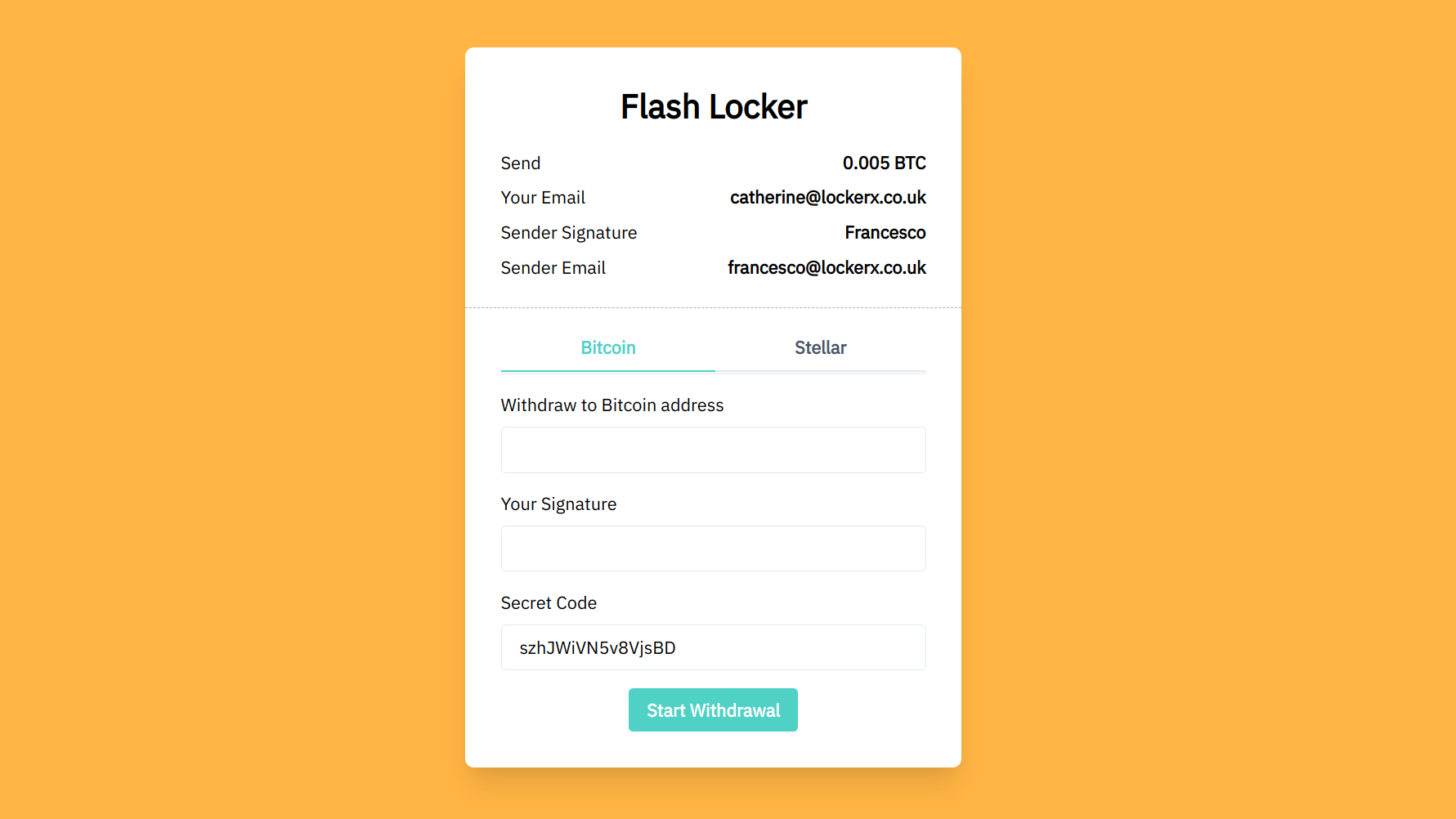
After filling out and reviewing their information, they will receive the payment to their wallet. That’s it!
If you noticed you made a mistake, for example you sent the wrong amount or used the wrong email address, you can easily cancel the payment and send the crypto back to your account.
If you want to learn more about Flash Locker and see all available options, visit the Flash Locker documentation page .
How Flash Locker works
Flash Locker works by tokenizing your Bitcoins on the Stellar blockchain. When you deposit your Bitcoin into the Flash Locker, we issue a token on Stellar for the equivalent amount of Bitcoin, this token can be redeemed for the same amount of Bitcoin. The Flash Locker Stellar account is locked so that only users with the secret unlock token can use it. In more technical terms, we set the signer of the Flash Locker account to the hash of the unlock token.